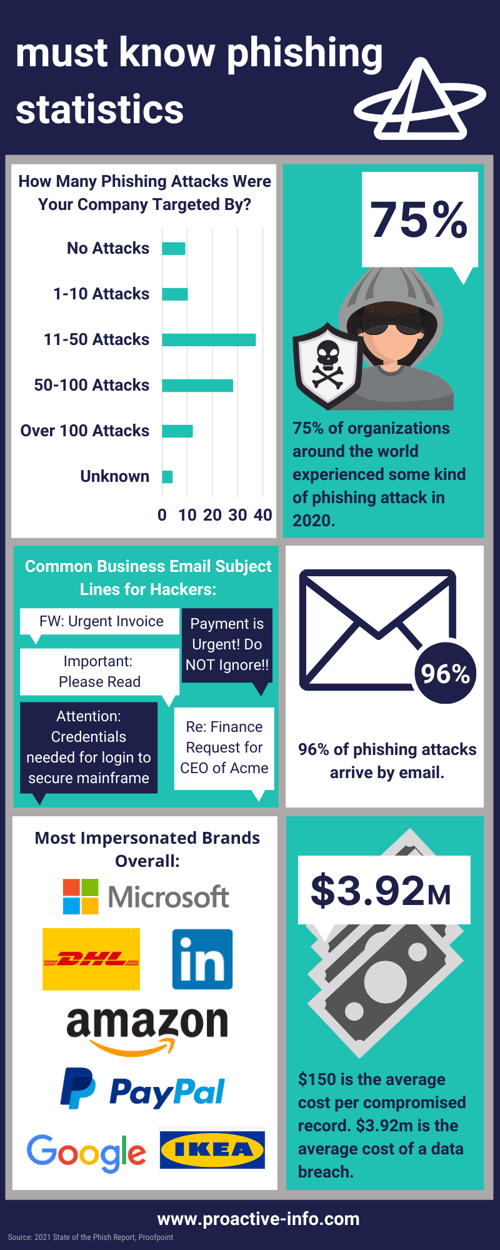
75% of organizations around the world experienced a phishing attack in 2020, and 74% of those attacks in the US were successful. Phishing attacks remain the most likely threat to cause a data breach.
phishing scams
Phishing attacks use social engineering in emails, ads and messages to persuade people to hand over valuable and sensitive information such as passwords, financial information, or access credentials. They can even persuade you to "Click Here" to download malware or complete a wire transfer. They continue to become more advanced and sophisticated and are a particular threat to the healthcare and financial industries.
how it happens
Almost all Phishing Scams are delivered by email, with less than 5% of attacks occurring through fraudulent websites, ads, or SMS communications.
According to Barracuda Network, the pandemic brought with it a staggering 667% spike in phishing emails. Almost 20% of employees are likely to click on phishing email links, and of those, an alarming 67% proceed to enter in their credentials on a phishing website! Hackers often use scare tactics like telling recipients that there are security alerts on their social media accounts, actions are required with their Amazon or banking accounts, and often use the phrases "Urgent!" or "Action Required".
who it effects
Simply put, everyone. But according to IBM, the healthcare industry is the most affected, followed by education and manufacturing.
the lasting consequences
The impacts of a phishing attack can be staggering, with the average cost of a data breach being in the millions. But financial losses are not the only negative outcomes of a data breach cause by a phishing attack.
Other losses can be:
- Loss of customers' personally identifiable information (PII)
- Loss of data
- Loss of business continuity
- Loss of intellectual property
- Damage to business reputation
- Compliance fines
- Remediation costs
- Loss of revenue and customers
- Legal fees
what can you do?
In addition to training your employees to follow email best practices, contact pim today to find out about their strong anti-phishing system that filters out phishing emails BEFORE they reach their intended recipient. pim's business IT solutions (bits) goal is to detect, protect, prevent, and resolve common network and system threats before they happen. Our advanced managed threat response, powered by SOPHOS, has advanced threat hunting, detection and response capabilities that take action to neutralize threats.