When you work in the financial industry, you are entrusted with properly managing and protecting your clients’ valuable assets in addition to maintaining compliance with many strict regulations and requirements. When extremely sensitive and valuable data is involved, including personally identifiable information (PII), banking and checking, credit card information and financial records, a data loss or breach can really jeopardize your reputation, harm customer loyalty, and could also result in hefty fines and legal repercussions. Additionally, a data loss or breach could equal downtime in your business operations that means further damage to your reputation and ability to serve your clients effectively.

Do You Know All of the Risks for the Financial and Banking Industry?
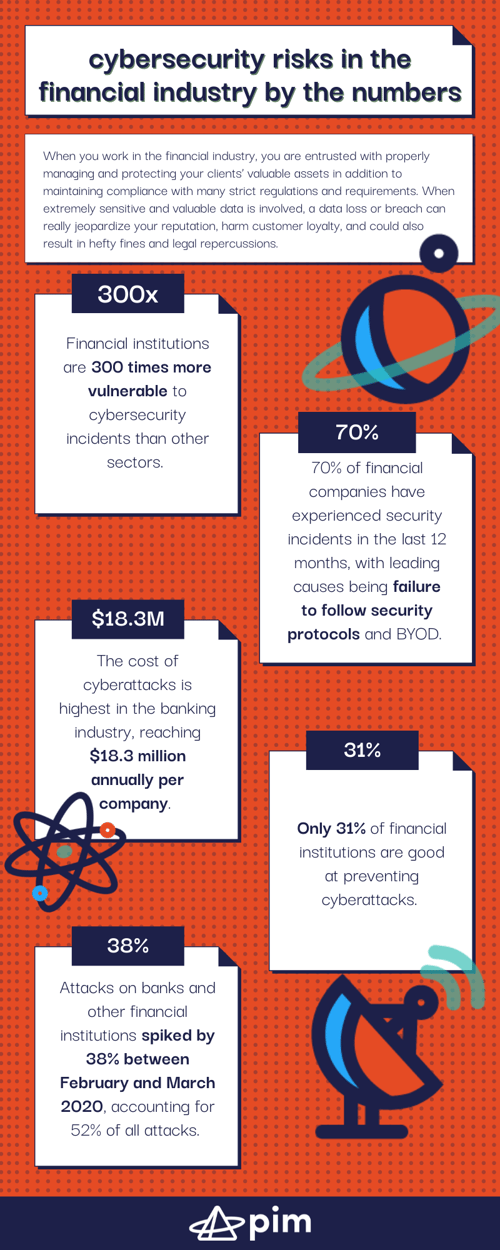 Here are some alarming stats pertaining to the financial industry:
Here are some alarming stats pertaining to the financial industry:
- Financial institutions are 300 times more vulnerable to cybersecurity incidents than other sectors. (Source: Boston Consulting Group)
- 70% of financial companies have experienced security incidents in the last 12 months, with leading causes being failure to follow security protocols and Bring Your Own Device policies. (Source: Clearswift)
- The cost of cyberattacks is highest in the banking industry, reaching $18.3 million annually per company. (Source: Accenture)
- Only 31% of financial institutions are good at preventing cyberattacks. (Source: Ponemon Institute)
- Attacks on banks and other financial institutions spiked by 38% between February and March 2020, accounting for 52% of all attacks. (Source: VMware’s Carbon Black Cloud)
Solutions to Address Common Challenges and Concerns
Next Generation Firewalls
Next Generation Firewalls (NGFW), intrusion detection systems (IDS), and intrusion prevention systems (IPS) not only inspect incoming/outgoing network traffic but add crucial security features like application awareness and control, intrusion prevention/detection, and cloud-delivered threat intelligence.
Threat Detection and Response
Threat Detection and Response (TDR) services recognize and respond to malicious activity fast, offering 24/7 monitoring and threat isolation—the sooner a threat is detected, the quicker action can be taken, lowering the chances of catastrophic results.
Security Information and Event Management
Security Information and Event Management (SIEM) tools log all incident files, filter out false positives, and present valid warnings and alerts in one central, unified view for quick and efficient triage.
Vulnerability Scans
Vulnerability Scans identify open ports, vulnerabilities, unusual traffic patterns and can tighten up cybersecurity plans.
Strong BYOD Policies
Strong BYOD Policies and approved whitelist apps help prevent data breaches caused by employees using personal devices; ongoing employee training and education is strongly recommended with human error accounting for 32% of attacks and 24% of unauthorized data shares.
Endpoint Security
Endpoint Security ensures computers, laptops, phones, or tablets, have the latest protection from viruses, trojans, malware, spyware, and other malicious advanced persistent threats.
Two-Factor Authentication
Two-Factor Authentication requires two types of credentials for authentication before an end-user is granted access, adding a layer of validation, reducing a threat actor’s attack surface and ability to gain unauthorized access to a sensitive data.
Managed Security Services
Managed Security Services lend enterprise-level security expertise, commonly offering 24/7 protection, multi-layered defense approach and specialized compliance solutions following NIST, ISO, ISACA, and FFEIC guidelines and GLBA and SOX standards.

Threats to IT Security constantly evolve therefore your organization’s plans and security postures should be reviewed with regularity in order to identify vulnerabilities and avoid data breaches. Regular risk assessments are part of developing an effective business continuity plan.