Hacking refers to activities that seek to compromise digital devices, such as computers, smartphones, tablets, and even entire networks. And while hacking might not always be for malicious purposes, most references to hacking, and hackers, include unlawful activity by cybercriminals—motivated by financial gain, protest, information gathering (spying), and even just for the “fun” of the challenge.
Hackers typically attempt to gain access to infrastructure, steal your data and, in most cases, profit from it. They accomplish this through a variety of means, and one of the most common ways is through Phishing. By responding to an email, opening up an attachment, or clicking on a link in a phishing email, the cybercriminal can then download or runs malware on your computer. Once malware is installed, they attempt to find any data that could be useful, such as financial information, personable identifiable information, or trade secrets. Typically, they will ‘encrypt’ your device so you can't access your data and then ransom it back to you.
Hacking can cause several issues from disruption in customer service, loss of financial and personal data, lost revenue, litigation, loss of reputation and even closing a business.
There are three basic types of hackers:
1. Black Hat -- The Bad Guys
Black hats are anyone attempting to gain access to infrastructure or data with malicious intent. Inflicting damage on systems, ransomware data, or selling information to the highest bidder, obtaining trade secrets, or just causing a disruption in service. Black hats who steal personal information from person or government websites often sell the data they obtain in black markets on the Internet or the "dark web". They're sometimes sold in bulk and priced per record.
2. White Hat -- The Good Guys
White Hat hackers, sometimes called ethical hackers, typically have authorization to attempt to breach defenses, perform penetration testing and work within a prescribed set of pre-determined rules. They are legally permitted to do so and work with individuals or organizations to identify vulnerabilities and make recommendations. Companies hire these types of hackers from cybersecurity groups to test their systems and determine whether or not a breach is possible.
Hacking, in this context, is deemed both a necessity and a risk. Certifications and qualifications are needed for a person to practice white hat hacking “professionally.”
3. Grey hat – Good or bad, depends upon who you ask.
Gray hats are like Black hats, but usually without the malicious intent. They often combine the intent and skills of both black and white hats. Just like ethical hackers, they hack into a system to point out vulnerabilities. However, like black hats, they do this anonymously and usually without the permission of the owners. Gray hat hackers do not take advantage of the identified vulnerabilities, instead choosing to inform the owners once they are done. The classic 80’s film War Games is about once of the most famous Gray Hat hackers, Kevin Mitnick and how he hacked the North American Defense Command (NORAD) who now fully operates as a White Hat.
What are the different types of hacking?
There are several types but the most common are:
Social Engineering
Social engineering is when hackers get you to release personal information to strangers usually by impersonating a trusted source.
Phishing
Phishing is a type of social engineering by email. Asking you to respond with information, open an attachment or click on a link to an external site to download malware.
Brute force
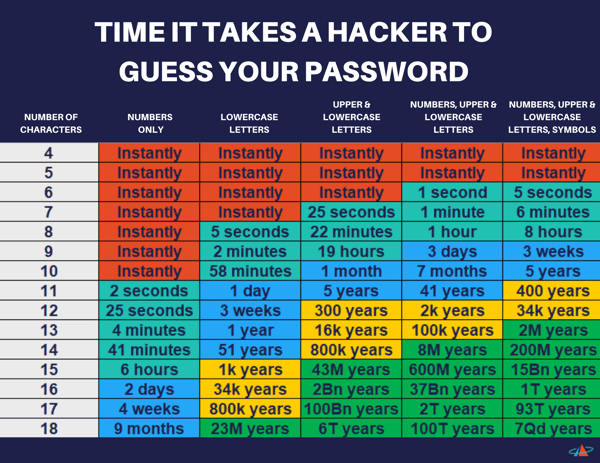
Brute force is when hackers use tools or manual attempts to guess possible combinations of a password until it is discovered. Weak passwords can take seconds to identify.
How can I prevent hacks?
- Education is the best defense when preventing hacking. Knowing how the actors work, the tools and means they will attempt to gain access to your systems or what to look out for in suspected Phishing scams will go a long way. Pim can conduct a phishing campaign where a sample of your employees will be tested and you will be provided a report and recommendations. Additionally, making sure that all employees are aware of email best practices can reduce the risk that phishing scams occur.
- Ensure all security patches and system updates are installed in a timely manner. This goes for desktops, laptops, tablets, cell phones, and smart TV’s (IoT – Internet of Things). Anything that can connect to the internet.
- Don’t give out personal information to strangers, whether its online or in person. Shred sensitive documents when you're finished with them and use strong passwords that change periodically without using the same password for multiple websites or applications. A password that is long, utilizes both upper case and lower case letters, as well as numbers and symbols is your best bet.
While putting in place effective passwords, firewalls, and effective IT security protocols are important steps to take in preventing hacks to your systems, devices, and networks, it is vital that you remember the human factor. Hackers are humans and your efforts to stop them must include educating the humans who work for you to recognize their actions. Your employees are both your weakest link and your strongest asset.