Malware and Computer Worms
Malware is malicious software that gains access to your computer to cause harm and destroy your...
The Sophos 2022 Threat Report identifies key trends in cyberthreats and adversary behavior that will impact IT security over the coming year. Understanding these trends helps pim develop security strategies for protecting your organization in 2022. It helps us to know where to focus our resources to best protect network, endpoint, and employees; to identify skill gaps; and where to add external threat hunting or incident response services for 24/7 coverage.
The Sophos 2022 Threat Report was written by a combined team from across SophosLabs, the threat hunting experts in Sophos Managed Threat Response (MTR), Sophos' MDR service, the incident responders in Sophos Rapid Response, and the Sophos AI team.
The Sophos 2022 Threat Report identifies several key trends that will impact IT security strategies into 2022 and beyond. These are not “predictions,” but robust, evidence-based developments based on the first-hand research, analysis and insight of Sophos researchers, threat hunters, incident responders, and data scientists during 2021.
This article covers each of these trends in turn.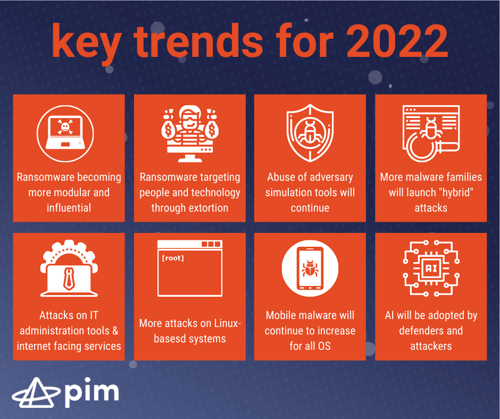
Over the past 18 months, pim’s partners, the Sophos Rapid Response team, has investigated and remediated hundreds of cases worldwide – and, as the pie chart shows, ransomware was involved in 79% of those incidents. As we move into 2022, the ransomware threat shows no sign of slowing down.
The biggest change in the ransomware landscape observed in 2021 is the shift away from adversary groups who make and then attack organizations using their own ransomware, towards a modular structure where every aspect of an attack is available for hire (such as the malicious code) or purchase (tools, targets etc.)
.png?width=500&name=Screenshot%20(1988).png)
Some of the most high-profile ransomware attacks of 2021 involved Ransomware-as-a-Service (RaaS), including an attack against Colonial Pipeline in the U.S. by a DarkSide affiliate.
We expect that RaaS developers will continue to invest time and energy in creating sophisticated code and determining how best to extract the largest payments from victims, insurance companies, and negotiators.
Sometimes, the developers also provide “attack playbooks,” detailing tools and techniques that help attackers to implement an attack – with the result that attacks by different affiliates can look very similar.
Once they have the malware they need, RaaS affiliates and other ransomware operators can turn to Initial Access Brokers (IABs) and malware delivery platforms to find and target potential victims.
Ransomware-as-a-Service families dominated in 2021. Incident reports from Sophos Rapid Response reveal the dominance of RaaS groups during 2021..png?width=500&name=Screenshot%20(1991).png)
Conti, REvil, Ryuk, Ragnarok, LockBit, and DarkSide are (or were, in the case of the seemingly disbanded REvil and DarkSide) all RaaS operations, accounting for nearly 60% of the ransomware incidents that Sophos Rapid Response investigated.
The modular service-based approach to a ransomware attack is having a significant influence on the entire cyberthreat ecosystem.
Like the gravitational force of a black hole in space, ransomware will pull in other cyberthreats to create a massive, interconnected ransomware delivery system.
For instance, “commodity” cyberthreats such as loaders and droppers will be increasingly used to deliver ransomware (alongside or instead of other malicious payloads such as adware, click fraud, spam, financial malware, and more).
Pressure tactics such as the theft and release of data will increasingly form part of the overall ransomware threat.
These tactics to increase pressure on victims to pay the ransom are designed to distress individuals, worry or inconvenience customers and partners, publicly shame the company in the media, reduce investor confidence, and attract the attention of data privacy authorities. And sadly, back-ups alone are not enough of a defense against such ransomware behaviors.
Commercial attack (or penetration testing) tools emulate different elements of a cyber-attack. They are used by IT security teams to test the strength of their cyber-defenses. Unfortunately, these tools are also being used by adversaries for actual attacks.
Cobalt Strike is an example of such a tool. First released in 2012, Cobalt Strike is commonly used by penetration testers and corporate “red teams” as part of the “offensive security” toolbox to test an organization’s defenses. Cobalt Strike features a backdoor called “Beacon,” which can be configured in several ways to execute commands, download and execute additional software, and relay commands to other Beacons installed across a targeted network.
The code for Cobalt Strike was leaked online and many pirated copies exist. Cybercriminals have been quick to seize the opportunity to use Beacons to gain a foothold on an infected machine.
We anticipate this trend will continue and that, during 2022, more intrusions are likely to be powered by Beacons. pim expects cybercriminals to increase their abuse of other adversary simulation tools, such as mimikatz and PowerSploit. Defenders should check every alert relating to abused legitimate tools or combination of tools, just as they would check a malicious detection, as it could indicate the presence of an intruder in the network.
pim’s parther, Sophos, tracks the detection of more than 180 different attack tools. Like Cobalt Strike, many of these attack tools were intended for legitimate use by penetration testers or security researchers. For example, the password-extractor “mimikatz” was the attack tool most spotted by Sophos on Windows computers.
More malware distribution families will adopt hybrid attack techniques, where mass targeting is followed by careful filtering to pinpoint the desired targets for specific malware bundles/payloads.
Hybrid attacks lure in lots of people, but only fire off when the unlucky people who stumble into the trap meet certain criteria.
This makes some sense from the criminals' perspective: they can block malware analysts from continuing to probe their servers, and they also reduce suspicion by keeping the number of attacks relatively low, flying underneath the radar that might otherwise tip off security researchers or IT admins to a wider campaign.
In 2021, Sophos reported on Gootloader operating such attacks. The operators started with a broad-based attack using malicious SEO techniques, luring in potential victims who might be looking for a specific kind of document on Google. We expect to see a wider adoption of such hybrid techniques going into 2022 and beyond.
In 2021, Sophos researchers detailed a number of new threats targeting Linux systems. Sophos expects to see a growing interest in Linux-based systems during 2022, both in the cloud and on web and virtual servers. Linux-based Internet-of-thing devices will also be targets of attack. We expect attacks targeting vulnerable Linux servers and commodity consumer electronics to continue unabated in 2022.
Cyber attackers will continue to exploit software vulnerabilities to mass-abuse IT administration tools and internet facing services.
Going into 2022, we expect to see continued, unpredictable attempts at the mass-abuse of IT administration tools and exploitable internet facing services like Exchange, by both sophisticated advanced persistent threat (APT) actors as well as by run-of-the-mill cybercriminal elements.
Mobile threats and social engineering scams, including Flubot and Joker, are expected to continue and diversify to target both individuals and organizations.
Flubot (a credentials/contacts and bank info stealer that spreads, among other things, via fake messages from delivery/courier companies) will continue to dominate the list of mobile malware for Android devices, and other malware may try to emulate its rapid distribution model.
More fraudulent apps will try to exploit loopholes in the iOS platform as the techniques become better known and understood by criminal groups..png?width=500&name=Screenshot%20(1994).png)
For example, “CryptoRom” is a fake iOS cryptocurrency scam targeting users of popular dating sites around the world. The scam spread its fake apps through iOS “test” platforms that developers can use to pre-test business and consumer apps before submitting them to the App Store for approval. Many Android malware families, such as Joker, evade detection by Google Play Store’s scanning tools using a simple trick: the apps uploaded to the Play Store don’t contain any malicious code themselves, but act as a delivery mechanism for a malware payload they only retrieve after you’ve installed the app.
These “droppers” act as a gateway for delivering many of the other categories of malware that Sophos detects on Android devices.
The application of artificial intelligence to cybersecurity will continue and accelerate, as powerful machine learning models prove their worth in threat detection and alert prioritization. The AI-driven security operations center (SOC) will start to become a reality: more efficient, intuitive and user-facing.
For instance, user-facing machine learning will make IT security products as intuitive at making security recommendations as Google is today at finding web pages or Netflix is at recommending content.
Supercomputer-scale neural networks will solve challenging security problems, such as automatic vulnerability identification and patching.
At the same time, however, adversaries are expected to make increasing use of AI, progressing over the next few years from AI-enabled disinformation campaigns and spoof social media profiles to watering-hole attack web content, phishing emails and more as advanced deepfake video and voice synthesis technologies become available.
What this means for security teams: security practitioners will need to keep pace with new AI innovations and find defensive applications of new AI ideas and technologies.
Malware is malicious software that gains access to your computer to cause harm and destroy your...
Ransomware is a type of malicious software, or malware, that prevents you from accessing your...
