With the increasing digitization of our world, both in our business and personal lives, it is now vitally important that organization’s do all they can to keep their data safe. The technologies that power our work are vital to business continuity efforts and so too is securing the data that flow through these technologies.

A Digital World Means Digital Theft
It used to be that the idea of someone stealing our money or hijacking our businesses meant something physical, like a burglary or a mugging. But today, if the proper safety measures aren’t put into place, we can be robbed while the attacker sits in soft pants from the safety of their couch and many times, we are unaware that the theft has even occurred.
The Most Common Threats
The biggest threats to your data often prey your weakest link: untrained employees.
Ransomware
In this type of cyberattack, a breach occurs when someone within your organization clicks on a link or file in an email, or hackers can crack your password. Once within your network, they unleash a program that essentially kidnaps or hijacks your computer and your data until you agree to pay a fee. If you don’t have the proper disaster recovery solutions in place, unless you are Liam Neeson and have a very particular set of skills, this means your business will likely have to pay the ransom in order to get your business back up and running.

Phishing
Phishing is the most attempted cybercrime. Phishing is essentially looking for people or habits that criminals can manipulate for their own personal game. In phishing scams, victims might get an email or text alerting them of a special offer or perhaps a problem they can fix. Often with research gleaned from social media accounts found easily online, these scams appear legitimate but are simply a ruse to get the victims to offer up willingly their credit card or credential information.
Ways to Protect Your Organization
Thankfully, there are ways to protect against these cyber threats. To be a secure business, you need to have safeguards in place in order to protect your data and the data of your clients and/or patients. Hiring a well-trusted MSP can help your organization stay on top of the latest threats and protects against disaster. Moving data and infrastructure to the cloud helps our business have stronger security and protective measures that generally make the storing of data and working in the cloud safer than with on-premise software and hardware that needs to be consistently updated.

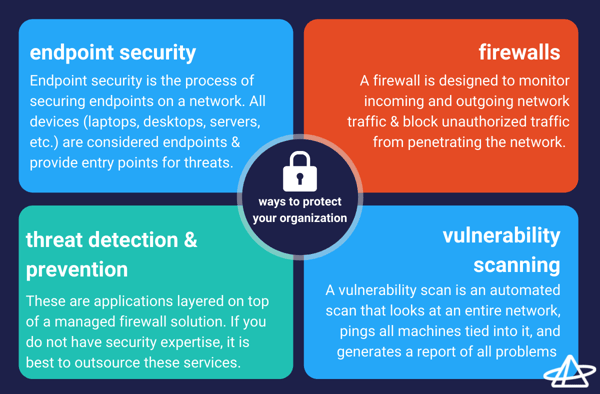
A sound security strategy has multiple layers. At a minimum, it should have the following in place: endpoint security, firewalls, threat detection and prevention, and vulnerability scanning.
Endpoint Security
Endpoint security is the process of securing endpoints on an organization’s network. All devices (mobile, laptops, desktops, servers) are considered endpoints and provide an entry point for threats. With the rise of BYOD and remote workforces, the need for endpoint security has increased significantly.
Firewalls
As the first required building block for an overall network security posture, a firewall is designed to monitor incoming and outgoing network traffic and block unauthorized traffic from penetrating the network. Maintaining a firewall requires a lot of time from IT resources, and the majority of businesses with a firewall don’t actively view the logs. A Managed Firewall is a realistic system for all businesses to have in place. The system gives a simplified view for easy filtering by ingress and egress traffic.
Threat Detection and Prevention
These are applications layered on top of a managed firewall solution. If your IT staff does not have security expertise, it is recommended to outsource these services.
- Threat Detection Services: Provide alerts when suspicious activity is detected and logs activity as an audit trail (does not take any actions to stop attack).
- Threat Prevention Services: Provides an increased layer of protection that helps to automatically defend against threats and attacks identified by the threat prevention services.
Vulnerability Scanning
A vulnerability scan is an automated scan that looks at a user’s entire network, pings all machines tied into it, and generates a report of all problems (like a building inspection). The report can include hundreds to even thousands of problems. It’s recommended to perform a vulnerability scan on a quarterly basis. Some organizations may be required to do this because of compliance.